Chapter 2:
Protocols
- What is a security protocol?
- How can we tell whether a security protocol is any good?
- "Grabber" story
- Protocol examples
- Problem: Entrance to secure facility
Protocol: Person must swipe their badge through
a machine and enter their PIN number. After the third consecutive
failure to enter the correct password, the person is considered a
spy and he/she is immediately shot by the security guard.
- Problem: How to protect my personal
information stored on my computer?
Protocol: ???
- Notation: {X}K means the value X
encrypted with key K.
Definition: A nonce is a "number used once". The purpose of a nonce
is usually to assure freshness (i.e., to prevent a replay attack).
- Parking garage protocol (simple authentication), where T
is the token
(or identifier) for the car, G is the parking garage, N
is a nonce
and KT is the key for token T
T → G : T,
{T, N}KT
Problems: How does G know KT? Which is better, a random nonce
or a sequence?
- Car door lock protocol (challenge-response): Let E be the engine
controller, T be the transponder in the car key, K the
cryptographic key and N a nonce.
E → T : N
T → E : {T, N}K
Problems: What happens if N is not very random?
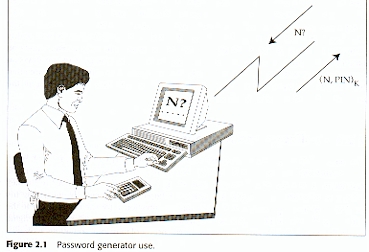
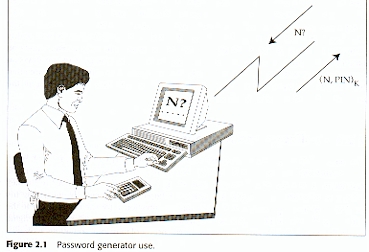
- Password generating protocol (challenge-response):
Let S be the server,
P the password generator, U the user, PIN the user's PIN number
and N a random nonce. Then
S → U : N
U → P : N, PIN
P → U : {N,
PIN}K
U → S : {N,
PIN}K
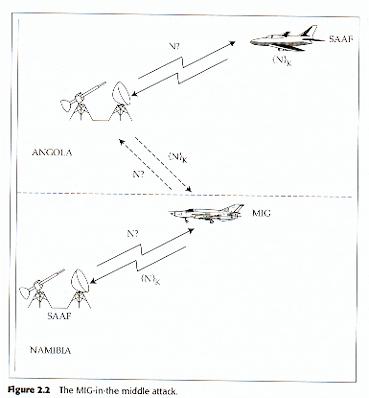
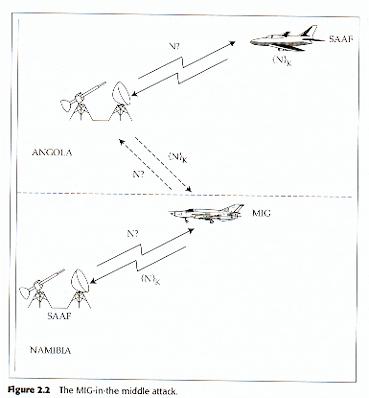
- MIG-in-the-middle (example of a "Man-in-the-middle", or MIM, attack):
An IFF system
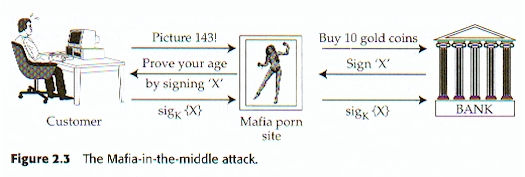
- Reflection attacks --- mutual authentication
- Manipulating the message
- Changing the environment
- Chosen protocol attack
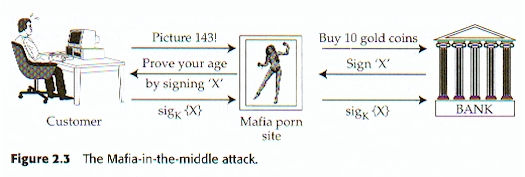
- Smartcard banking protocol: Let C be the customer
account number, NC the customer transaction
number, K the key and X the electronic check. Then
C → R :
{C, NC}K
R → C :
{R, NR, C,
NC}K
C → R :
{C, NC,
R, NR, X}K
- Managing crypto keys --- discuss this after chapter on cryptography
Chapter 2 homework problems
and solutions