










More Locking, Start Time Stamp Scheduling
CS157b
Chris Pollett
Apr 17, 2023











CS157b
Chris Pollett
Apr 17, 2023
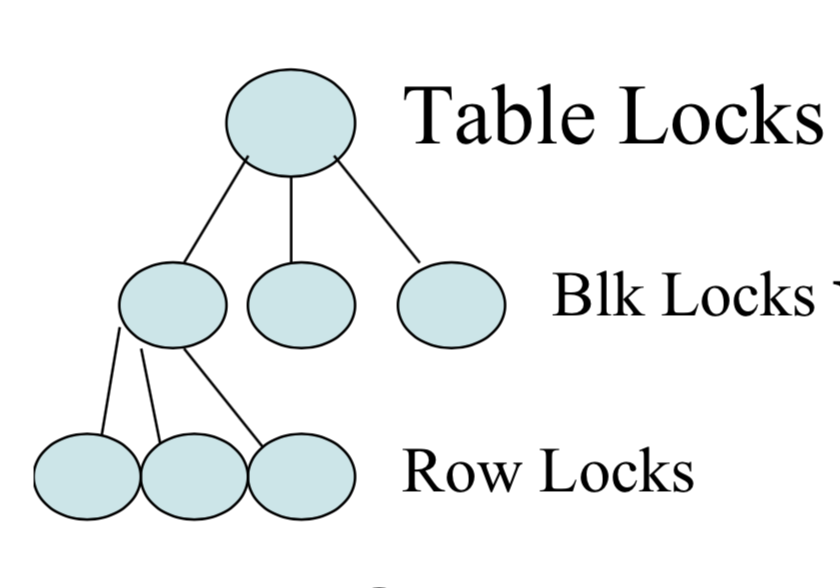
| Lock Requested | |||||
|---|---|---|---|---|---|
| IS | IX | S | X | ||
| Lock Held in Mode | IS | Y | Y | Y | N |
| IX | Y | Y | N | N | |
| S | Y | N | Y | N | |
| X | N | N | N | N | |
Which of the following statements is true?
SET TRANSACTION READ ONLY; SET TRANSACTION READ WRITE;