










More Database Services
CS185c
Chris Pollett
Feb. 18, 2010
(These notes are based on slides which are copyright IBM)











CS185c
Chris Pollett
Feb. 18, 2010
(These notes are based on slides which are copyright IBM)
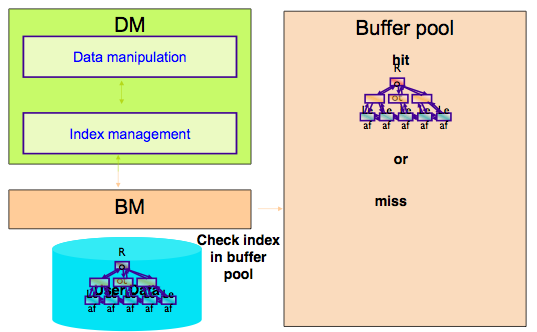
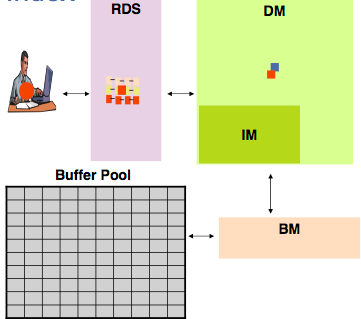
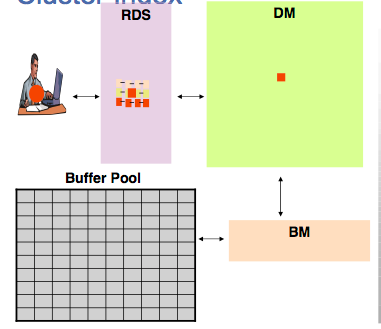
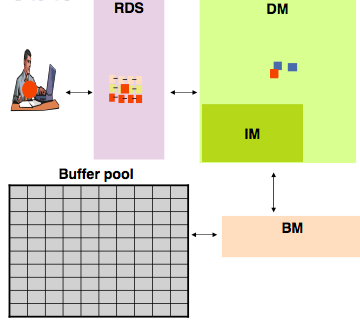
Here are the major operations that the BM needs to perform and the algorithm or data structure used to do it: