Authentication Protocols
CS166
Chris Pollett
Oct 31, 2012











CS166
Chris Pollett
Oct 31, 2012
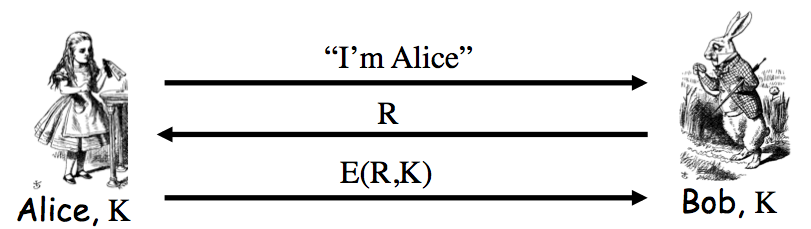
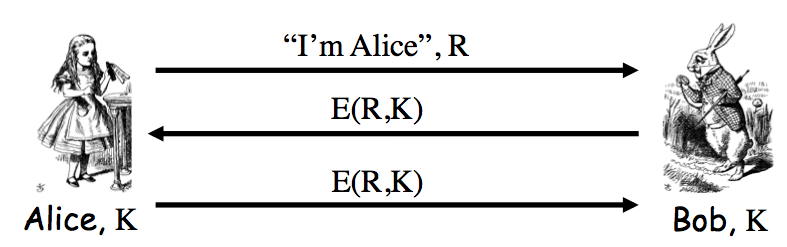
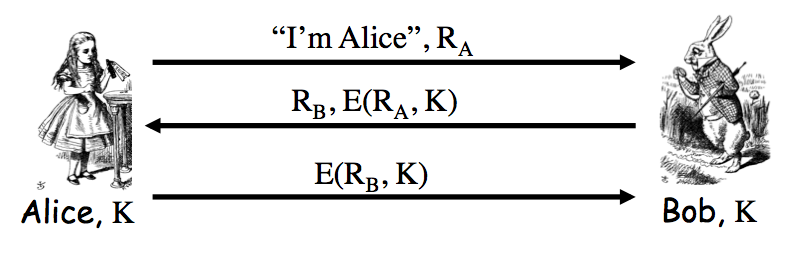
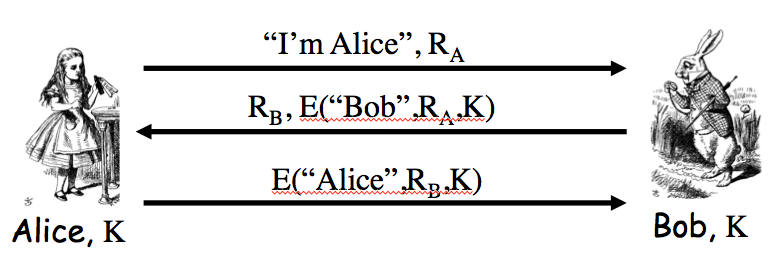
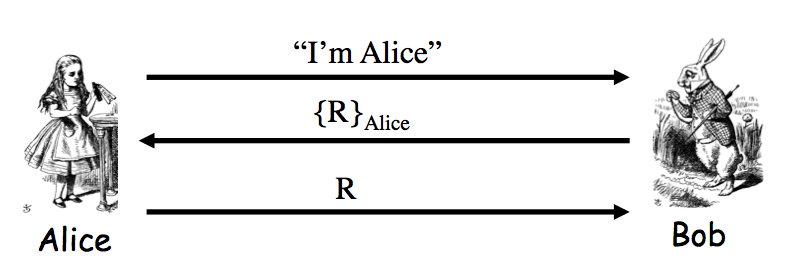
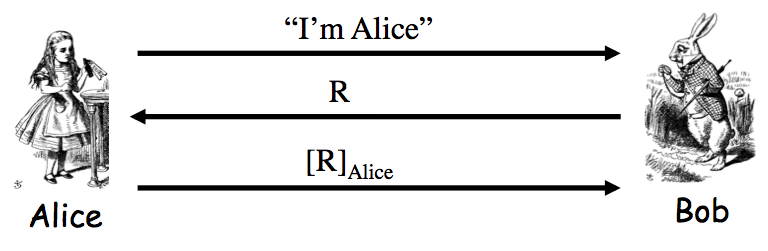
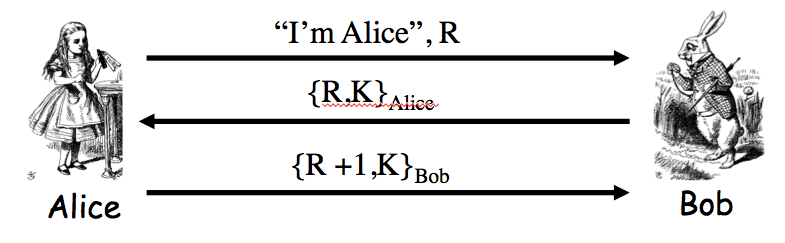
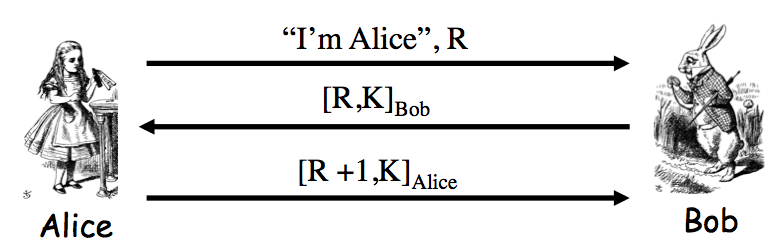
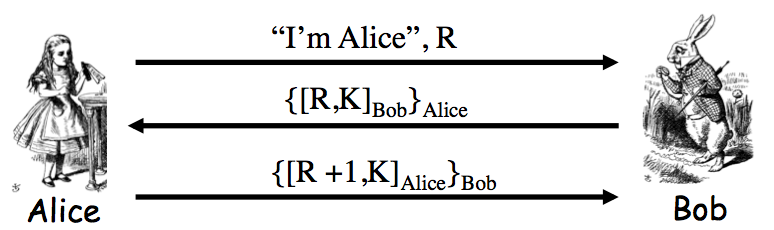
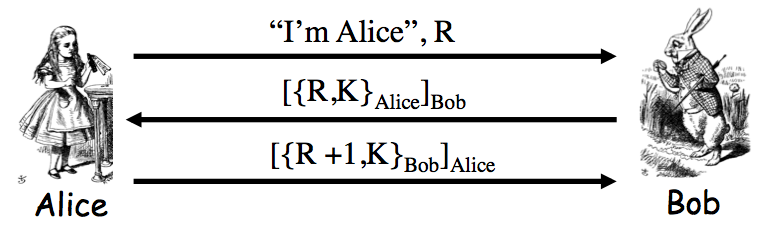
Problem 9.4 Consider the following mutual authentication protocol, where `K_(AB)` is a shared symmetric key.
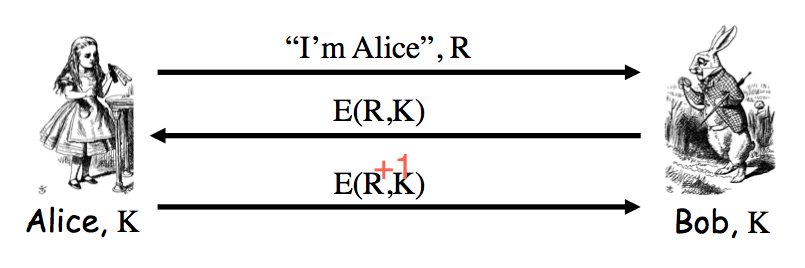
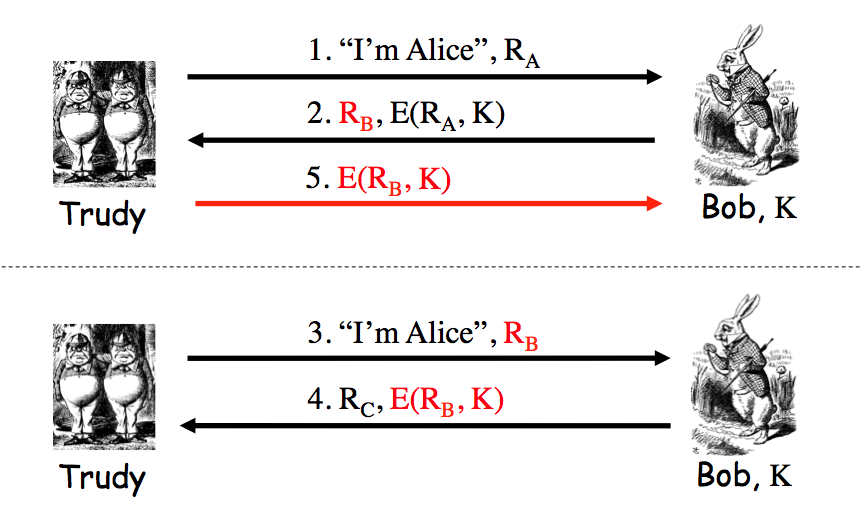
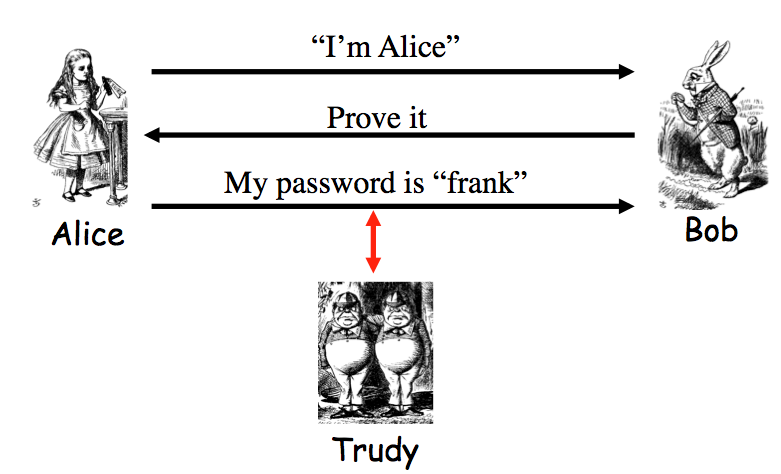
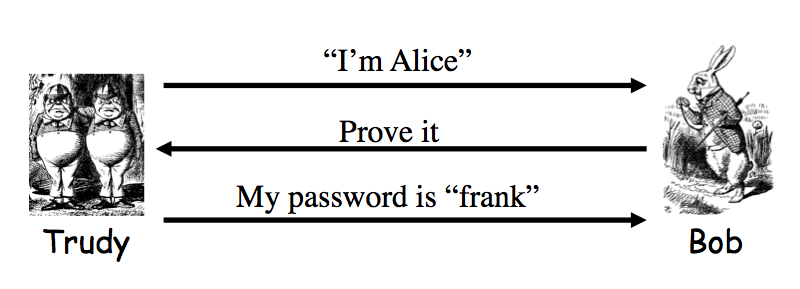
Give two different attacks that Trudy can use to convince Bob that she is Alice.
Answer. Trudy could send the message "I'm Alice, R + 1". Then when Bob sends `E(R+1, K_(AB))`, Trudy sends the message "I'm Alice, R". When Bob sends `E(R, K_(AB))`, Trudy can reply with `E(R+1, K_(AB))` she saw earlier. Alternatively, if Trudy watched the complete exchange of Alice and Bob, she could just replay all the messages.