Crypto Terms, Simple and Double Transposition Ciphers
CS166
Chris Pollett
Aug. 27, 2012











CS166
Chris Pollett
Aug. 27, 2012
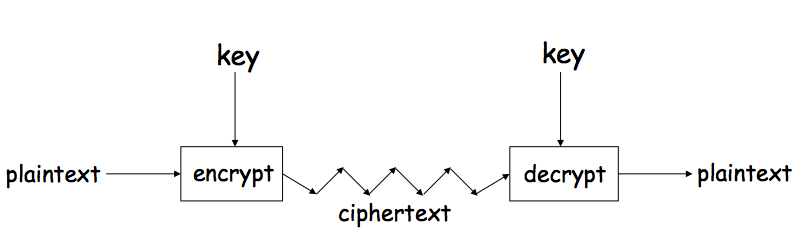
A generic view of symmetric key crypto
We next study cryptography a little by looking at an example of a special case of a substitution cipher...
Plaintext: abcdefghijklmnopqrstuvwxyz Ciphertext: DEFGHIJKLMNOPQRSTUVWXYZABC
Which of the following is true?
We can generalize Caesar's shift-by-three cipher to a shift-by-n cipher...
Plaintext: abcdefghijklmnopqrstuvwxyz Ciphertext: HIJKLMNOPQRSTUVWXYZABCDEFG
Plaintext: abcdefghijklmnopqrstuvwxyz Ciphertext: JICAXSEYVDKMBQTZRHFMPNULGO
PBFPVYFBQXZTYFPBFEQJHDXXQVAPTPQJKTOYQWIPBVWLXTOXBTF XQWAXBVCXQWAXFQJVWLEQNTOZQGGQLFXQWAKVWLXQWAEBIPBFXF QVXGTVJVWLBTPQWAEBFPBFHCVLXBQUFEVWLXGDPEQVPQGVPPBFT IXPFHXZHVFAGFOTHFEFBQUFTDHZBQPOTHXTYFTODXQHFTDPTOGH FQPBQWAQJJTODXQHFOQPWTBDHHIXQVAPBFZQHCFWPFHPBFIPBQW KFABVYYDZBOTHPBQPQJTQOTOGHFQAPBFEQJHDXXQVAVXEBQPEFZ BVFOJIWFFACFCCFHQWAUVWFLQHGFXVAFXQHFUFHILTTAVWAFFAW TEVOITDHFHFQAITIXPFHXAFQHEFZQWGFLVWPTOFFA
This kinds of codes were broken before computers, so we know it can be done -- we just have to clever.
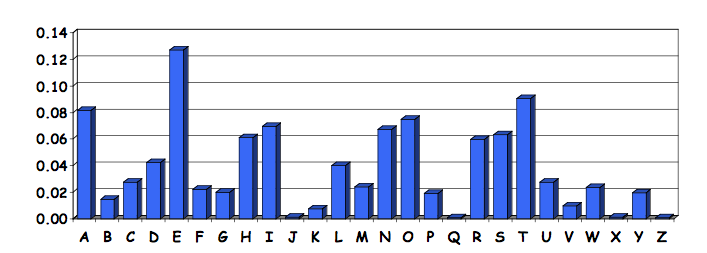
Looking at the frequency counts for:
PBFPVYFBQXZTYFPBFEQJHDXXQVAPTPQJKTOYQWIPBVWLXTOXBTF XQWAXBVCXQWAXFQJVWLEQNTOZQGGQLFXQWAKVWLXQWAEBIPBFXF QVXGTVJVWLBTPQWAEBFPBFHCVLXBQUFEVWLXGDPEQVPQGVPPBFT IXPFHXZHVFAGFOTHFEFBQUFTDHZBQPOTHXTYFTODXQHFTDPTOGH FQPBQWAQJJTODXQHFOQPWTBDHHIXQVAPBFZQHCFWPFHPBFIPBQW KFABVYYDZBOTHPBQPQJTQOTOGHFQAPBFEQJHDXXQVAVXEBQPEFZ BVFOJIWFFACFCCFHQWAUVWFLQHGFXVAFXQHFUFHILTTAVWAFFAW TEVOITDHFHFQAITIXPFHXAFQHEFZQWGFLVWPTOFFA
We get:
A B C D E F G H I J K L M N O P Q R S T U V W X Y Z 21 26 6 10 12 51 10 25 10 9 3 10 0 1 15 28 42 0 0 27 4 24 22 28 6 8
So we might guess F represents the letter e; Q, the letter T; and so on for the most frequent letter. One checks if the decryptions make sense and work back-and-forth to get more of the letters.