Outline
- Wireshark
- Interdomain Routing
- IPv6
Wireshark
- We pause for a moment on the problem of routing to look at another network tool.
- Wireshark (http://www.wireshark.org/) is a free packet sniffer much like tcpdump but with a graphical front-end.
- It has a nice interface to easily allow you to look at Ethernet frames, IP packets, as well as, Wireless, TCP and UDP, etc. traffic.
- It used to be called Ethereal but the name was changed in 2006 because of trademark issues.
Using Wireshark
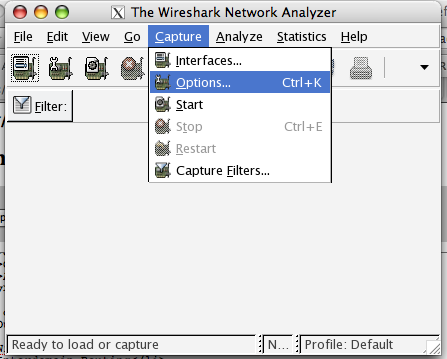
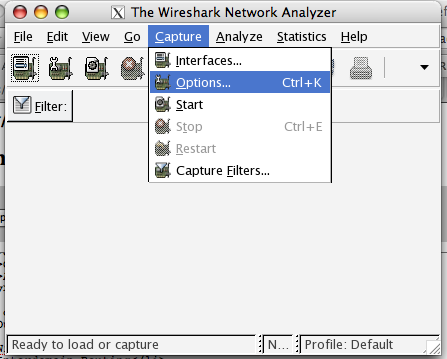
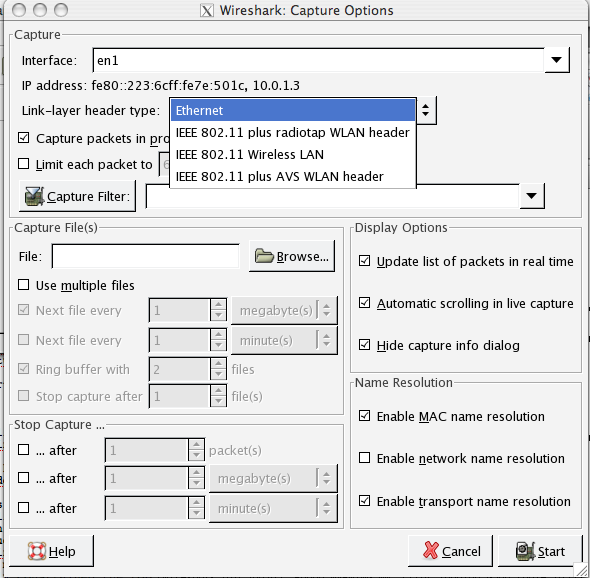
- After starting Wireshark with sufficient privileges to access the interfaces you want to look at, you can click on Capture > Options to set up the kind of traffic capture you want to do.
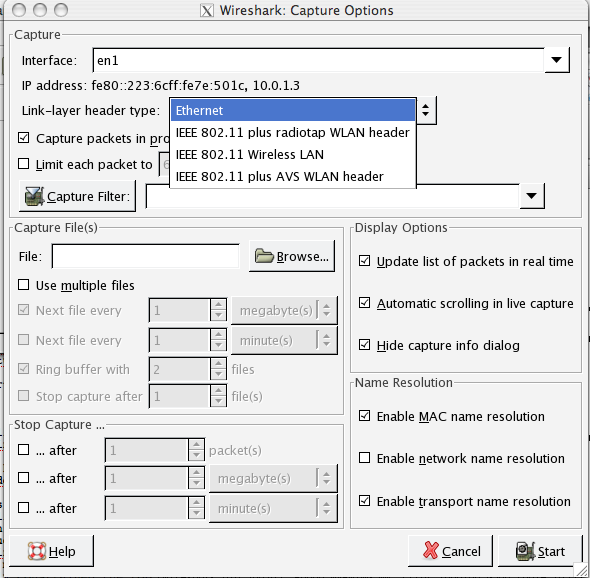
- Notice you can also set a Capture Filter if you want. This would allow you to say just capture TCP traffic, or even further restrict the traffic you are looking at. For instance, you might want to look at just HTTP traffic to some host.
- Once you have set-up the options as you like, you can use Capture > Start and Capture > Stop to begin/end recording traffic.
- You can then either look at this traffic manually, by clicking on the packets you would like to look at in more detail or you can use the Analyze and Statistics menus to automate analyzing what you are seeing.
Interdomain Routing
- So far we have looked at routing within autonomous systems (AS's) (aka domains), that is, internetworks under a single administrative control.
- The interdomain routing problem is the problem of having different AS's share reachability information -- the IP addresses that can be reached via a given AS.
- Each AS is allowed and needs to be able to set its own routing policies.
- Such a policy might be to always prefer to send traffic via AS X versus AS Y, perhaps because, your AS gets a cheaper rate for sending traffic
over AS X than over AS Y.
- Other issues might be you can't send traffic through such and such country.
- Whatever interdomain routing procedure is used, it needs to support such policies.
- The first major interdomain routing protocol was the Exterior Gateway Protocol (EGP).
- It severely constrained the topology of the AS's into a tree.
- Its replacement is the Border Gateway Protocol (BGP) which we'll consider next.
The Multi-backboned Internet
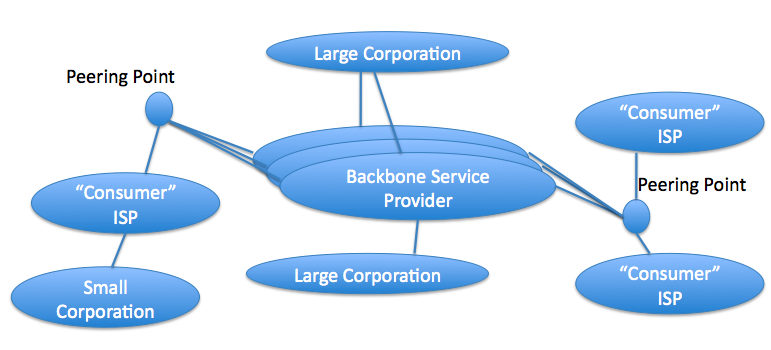
- Unlike EGP, BGP supports multiple backbone networks. These are usually called service provider networks.
- The topology of today's network might be abstracted as:
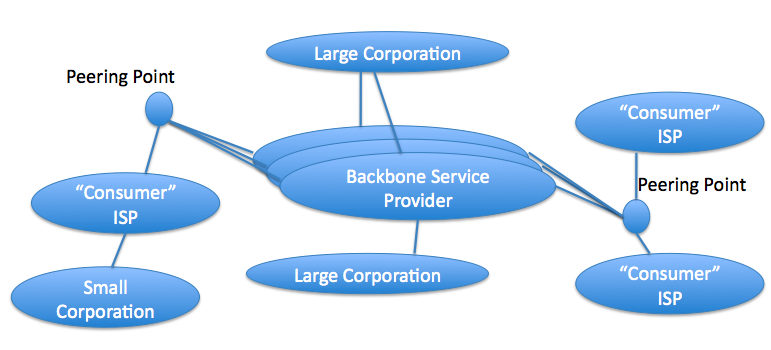
- Given this view of the internet, we define local traffic as traffic that originates and terminates within an AS; and we define
transit traffic as traffic that passes through an AS.
- We can classify AS's into three types:
- Stub AS - an AS that has only one single connection to one other AS. For example, a small corporation in the above
- Multi-homed AS - an AS that has connections to more than one other AS, but that refuses to carry transit traffic. A large corporation might be an example of this.
- Transit AS - an AS that has connections to more than one other AS and that is designed to carry both transit and local traffic. An example of this might be a backbone provider.
Challenges of Interdomain Routing
- Scale - a backbone router must be able to forward any packet destined anyway on the internet. CIDR helps
control this, but still there on the order of a couple hundred thousand of valid address prefixes.
- Difficulty in Computing Path Costs - each AS might be using a different interior routing protocol,
each with their own path metrics. So it is hard to combine these into one cost. Instead, interdomain routing
advertises only path reachability.
- Trust - Provider A might not believe certain advertisements from Provider B. For instance, B might be
misconfigured to say it supports routes to anywhere. This often means having policies of the form:
"use AS X to reach prefixes p and q, if and only if AS X advertised reachability to these prefixes."
BGP
- When configuring BGP, the administrator of each AS picks at least one node to be a BGP speaker, this
is essentially the spokesperson for the entire AS.
- The BGP speaker establishes BGP sessions to other BGP speakers in other AS's.
- Who a BGP speaker knows is a neighbor they can talk with is manually configured.
- Speakers send keep-alive messages every 60 seconds or so to keep the connections to their neighbors.
- BGP sessions are used to exchange reachability information among AS's
- In addition to BGP speakers, the AS has one or more border gateways, these are routers through which packets
enter or leave the AS.
- Unlike distance-vector or link-state, BGP advertises complete paths as an enumerated list of AS's to reach a
particular network.
- The complete path is needed to enable checking against a given AS's policies.
- It also makes it easy to check for routing loops.
BGP Example
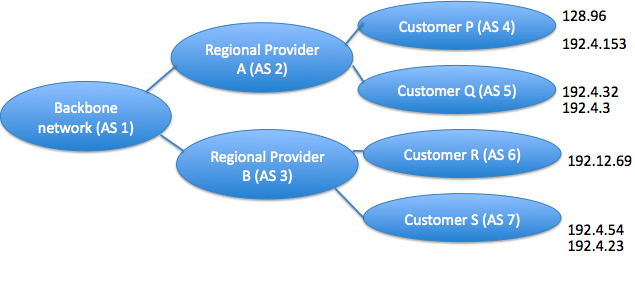
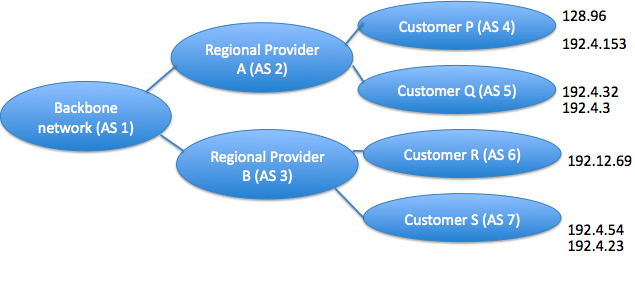
- Assume in the above that providers are transit networks, customers are stubs.
- A BGP speaker for the AS of provider A (AS 2) would be able to advertise reachability information for each of the network numbers assigned to customers P and Q.
- So it would say: "128.96, 192.4.153, 192.4.32, and 192.4.3 are directly reachable from AS2."
- The Backbone network AS 1 can advertise something like: "128.96, 192.4.153, 192.4.32, and 192.4.3 can be reached along (AS1, AS2)."
- It can also advertise : "192.12.69, 192.4.54, and 192.4.23 can be reached along (AS1, AS3)."
More on BGP
- One important job of BGP is to prevent loops.
- Suppose AS1 learns that it can reach 10.0.1 through AS 2, so it advertises this to AS 3, who in turn advertises this back to AS 2.
- AS 2 might decide that AS 3 was the place to send packets destined for 10.0.1. AS 3 would then send them to AS 1 who would send these packets back to AS 2, letting them loop forever.
- This does not happen because advertisements carry the complete AS path. So AS 2 would realize that the route come back to itself because
the route would be advertised as (AS 3, AS 1, AS 2).
- For this to work of course AS numbers carried in advertisements must be unique.
- These numbers are 16 bits long and are assigned by a central authority to assure uniqueness.
- Although 65000 numbers is not that many, since AS stub addresses don't need to be unique, this is more than enough.
- If a BGP speaker has a choice of several different routes to a destination, it will choose the best amongst these according to its own local policies.
- A BGP speaker is under no obligation to advertise a route to a destination even if it has one.
- BGP also supports negative advertisements if a route needs to be withdrawn.
- BGP runs on top of TCP, and counts on the fact that TCP provides reliable transport of data.
Integrating Interdomain and Intradomain Routing
- Let's look now at how Interdomain and Intradomain Routing interact.
- In the case of a stub AS, the border router is the only choice for routes out of the AS.
- Such a router can inject a default route in the intradomain routing protocol, so that
any network not explicitly advertised in the intradomain protocol is reachable through the border router.
- A border router of a provider AS might learn either through BGP or through configuration that some networks
are in a given customer AS.
- It could then inject a route to that prefix into the routing protocol running inside the provider AS.
- A border router in the backbone does not use injection, as given the number of prefixes this would be too costly.
- Instead a variant of BGP called interior BGP (iBGP) is used.
- iBGP allows any backbone router to learn the best border router to use when sending a packet to any address.
- In a brain-dead set-up, iBGP would require a full mesh of speakers -- everyone speaker would need to maintain connections
to every other speaker.
- In practice, central point routers called route reflectors are typically peered with several BGP routers to reduce the number of connections. Confederations, which are sets of AS's grouped into one, are also used.
- A conventional intradomain routing protocol such as distance vector is used to allow a router to know how to
forward to that particular border router.
Routing Areas
- One thing to note: AS don't correspond to necessarily to OSPF areas.
- An internetwork using OSPF might all be one AS, so we would then have the hierarchy: area - AS - Internet
- The book abbreviates routers that border areas as ABRs (area border routers).
IPv6
- Despite using subnetting and CIDR the number of available IPv4 addresses is dwindling rapidly.
- To address this issue in 1991, the IETF began work on IPng (IP - the next generation), which later became IPv6.
- This project also accreted additional problems that it would try to solve, for instance, real-time services, security support,
autoconfiguration, and mobile host support.
- Although many of these things were absent from IPv4 when IPv6 was first designed there were added to it later.
IPv6 Addressing and Routing and Allocation
- IPv6 address are 8 two-byte numbers.
- So the address space is 128 bits as opposed to the 32 bits of IPv4.
- Like IPv4, IPv6 addresses are classless, but the address space is still subdivided in various ways based on the leading bits.
- These leading bits specify the kind of use of that particular IPv6 address:
- all 0's -- unspecified
- 127 0's 1 -- loopback
- 1111 1111 -- multicast address
- 1111 1110 10 -- link local unicast (unique to the given network)
- 1111 1110 11 -- site local unicast (unique to the given private internetwork)
- Everything else