Outline
OSPF
Mobile Routing
Routing Implementation
Link State Routing (OSPF)
- Last day, we looked at distance vector routing and RIP
- The second major class of intradomain routing protocols are those based on link state routing.
- The starting assumptions for these algorithms are similar to those for distance vector protocols: It is assumed
that each node is capable of finding out the state of its neighbors (up or down) and the cost of each link going out.
- Link state routing makes use of reliable flooding. This is the process of making sure that all nodes participating
in the routing protocol get a copy of the link-state information from all other nodes.
- To do this each node sends its link-state information on all of its directly connected links, with each node that
receives this information forwarding it out on all its links.
- This link-state information is sent out in a so-called link-state packet (LSP).
- Each node periodically calculates and sends out such packets.
- An LSP consists of: The identity of the sender, followed by a sequence number, a TTL, and then followed by a list of neighbors.
- After a router has been accumulating a set of link state
packets for a while, it can construct the entire subnet as
each link is represented in some link state packet.
- Dijkstra's algorithm can then be used to construct the
shortest paths to all possible destinations, this can be
installed in the routing tables, and normal operations can
be resumed.
Link State -- Filling in More of the Details
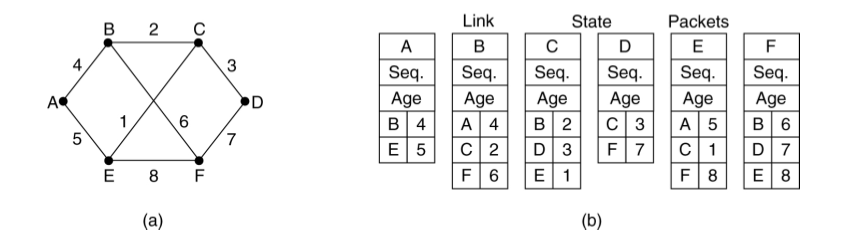
- As an example of LSPs for a specific graph consider:
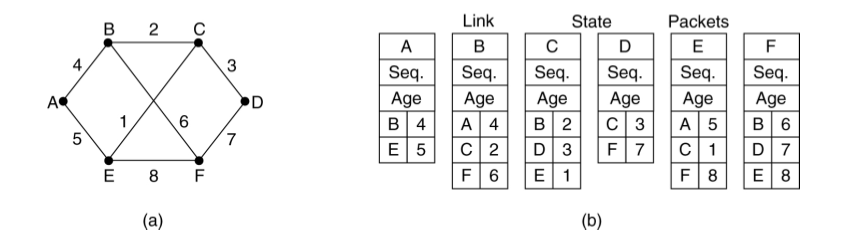
The link state packets for each router in the graph (a)
below are listed in (b).
- To avoid the flooding process continuing indefinately, routers keep track of
(source router, sequence) pairs and duplicates are
discarded. Only non-duplicates are forwarded using flooding.
- The sequence number is 32-bits or 64 bits so is unlikely to wrap before being
discarded.
- The TTL (aka Age) field is decremented once per second by the routers who are
remembering a particular router, sequence number pair, if it hits zero,
the router discards the entry. They also reflood this LSP with a TTL of 0. This
signals to other router to delete the entry.
- If a router goes down, it starts at sequence number 0 again. If it was down for
a long time, all the earlier packets will have timed out, and so this will be okay.
If it has only been down a short time, the router will eventually receive one of
its own packets from before it went down. If it does, it adds 1 to this LSP's
sequence number and refloods.
- All link state packets are acknowledged.
- It can be proven that the link state algorithm converges quickly, does not generate much traffic, and responds rapidly to topology changes.
Link State -- Dijkstra's Algorithm
- Dijkstra's algorithm (1959) can be used to find the shortest
path between two points in a graph, assuming we know its vertices, edges, and weights.
- For each node, the link-state packets give us this information.
- The algorithm works as follows
- Each node is initially labeled with its distance from the source along the
best known path. Node for which no path is known are labeled initially with
INFINITY.
- Nodes are also labeled temporary or permanent. Initially, the start node is
labeled permanent. We also have an active node which is initially the start
node.
- In a round, we update the distances to each of the nodes adjacent to
the active node, we then search the graph for the temporary node of
least distance, mark it permanent and set it as active. Then iterate
until no change.
Open Shortest Path First Protocol (OSPF)
- OSPF is one of the most common link-state routing protocols.
- Another link state protocol which was very influential was
IS-IS (Intermediate System - Intermediate System) which
was developed for DECnet and later used by ISO in its
connectionless network layer protocol, CLNP.
- Open in the name comes from the fact that the defining standards body, the IETF wanted this standard to be open (non-proprietary).
- SPF is an alternative name for link-state routing.
- (RIP) was replaced by OSPF sometime in the early 1990s as the main interior gateway protocol.
- OSPF supports several features not in the original link-state algorithm:
- Authentication of routing messages - this is to guard against a misconfigured host being able to claim that it is distance 0 from everybody.
- Additional hierarchy - to increase scalability of the internetworks that can be handled by this protocol domains can be further split into areas. i.e., routers within an area only need to be able to route within that area; not necessarily the whole domain -- a second layer of routers is used to route between areas.
- Load balancing -- OSPF allows multiple routes to the same place to be assigned the same cost and will cause traffic to be evenly distributed over those routes.
More on OSPF
- Domains are also called autonomous systems (AS).
- In OSPF, every AS has a backbone area, called area 0, and all other areas are
connected to this backbone (possible by tunnels).
- A tunnel is represented by an arc and has a cost.
- Each router connected to two or more areas is part of the backbone.
- Within an area each router has the same link state database and runs
the same shortest path.
- OSPF has three kinds of routes: intra-area, inter-area, and inter-AS.
- Intra-area routes are essentially computed using only link state.
- Inter-area routes are all computed in three steps: compute source to
backbone, backbone to destination area, destination area to final
destination.
- We'll talk about inter-AS routes later.
Even More on OSPF
- OSPF distinguishes four classes (allowed to overlap) of routers:
- Intra-area routers
- Area Border Routers connect two or more areas
- Backbone Routers are on the backbone
- AS boundary routers that talk to routers in other AS's.
- When a router boots it sends HELLO on each of its point-to-point lines and
multicasts them on LANs to the group of other routers on the LAN.
- OSPF works by exchanging information between adjacent routers.
- On each LAN one router is voted to be a designated router.
- Two routers are adjacent if they are on the same LAN and one is the
designated router. Only adjacent routers exchange information.
- Periodically each router floods LINK STATE UPDATE messages to each
of its adjacent routers.
- This has a sequence number to prevent it from propagating forever.
- These messages are also sent when a line goes up or down or changes cost.
- Other messages that are used are DATABASE DESCRIPTION, which
gives the sequence number of all link state entries currently held by the
sender. (Used when a line is brought up), LINK STATE REQUEST, and
LINK STATE ACKNOWLEDGEMENT.
Metrics
- We haven't discussed so far how to calculate the cost of links.
- We could always just give a cost of 1 to all links.
- This has the drawback that it doesn't taken into account the latency of
the link. For instance, a satellite link might have a large latency.
- It also doesn't take into account the capacity of the link.
- ARPANET, a precursor of the Internet, used the queue length of packets waiting
to be transmitted on each link as a metric for load on a link.
- This has the tendency of favoring the shortest queue, rather than actually than
actually measuring latency or capacity.
Routing for Mobile Hosts
- In a mobile setting, a host can become disconnected from one network and connected to a different one.
- An IP address on the other hand is supposed to indicate roughly when a host is in a network.
- One solution to this problem is to have the mobile device get a new IP address using something like DHCP.
- For some internet applications this might work: For instance, if all you were doing was requesting and receiving web pages.
- For other applications like Voice over IP it would probably cause the application to fail.
More Routing for Mobile Hosts
- The procedures to solve the problem of getting IP to work in the mobile setting are called Mobile IP and there is an IETF Mobile IP Working group dedicated to solving them.
- One technology introduced to support Mobile IP is the use of a home agent.
- This router is located on the "home" network of the mobile host.
- Each mobile host has a permanent IP address called its home address which has a network number equal to that of the home network.
- In addition, to the home agent, another special router called the foreign agent is also often used.
- Home and foreign agents use advertisements to announce their presence.
- The Home agent's advertisement enable the Mobile Host to learn its Home Network's address before it leaves that network.
- When the Mobile Host connects to a new network, it determines who is a foreign agent by listening for foreign agent advertisements. It then registers with the foreign agent for that network, telling the foreign agent what its home network is.
- The foreign agent then contacts the home agent providing a care-of address (the IP address of the foreign agent).
Sending and Receiving Mobile IP
- To send a packet, a mobile host sets the destination of the IP packet to where ever it wants to send, and it sets the source IP to its permanent IP address.
- For some other host B to send to the mobile host A, B uses A's permanent IP address as the destination.
- The Home agent, uses a technique called proxy ARP to impersonate the Mobile Host on the Home Network.
- It should be noted it only does this if A has registered with a foreign agent; otherwise, it just lets the packet go to A on the Home Network.
- Suppose the Home Agent receives the packet destined for A. In this case, it forwards the packet to the foreign agent by just wrapping the packet in another IP header with destination the Foreign Agent.
- The foreign agent unwraps this packet and sends it to the hardware (Ethernet) address registered with it by A.
- Sometimes to improve the performance of sending to the Mobile Host, the Home Agent can send a binding update message back to B with the care-of address of A.
- This allows B to directly send to A at this new address.